AI Cybersecurity
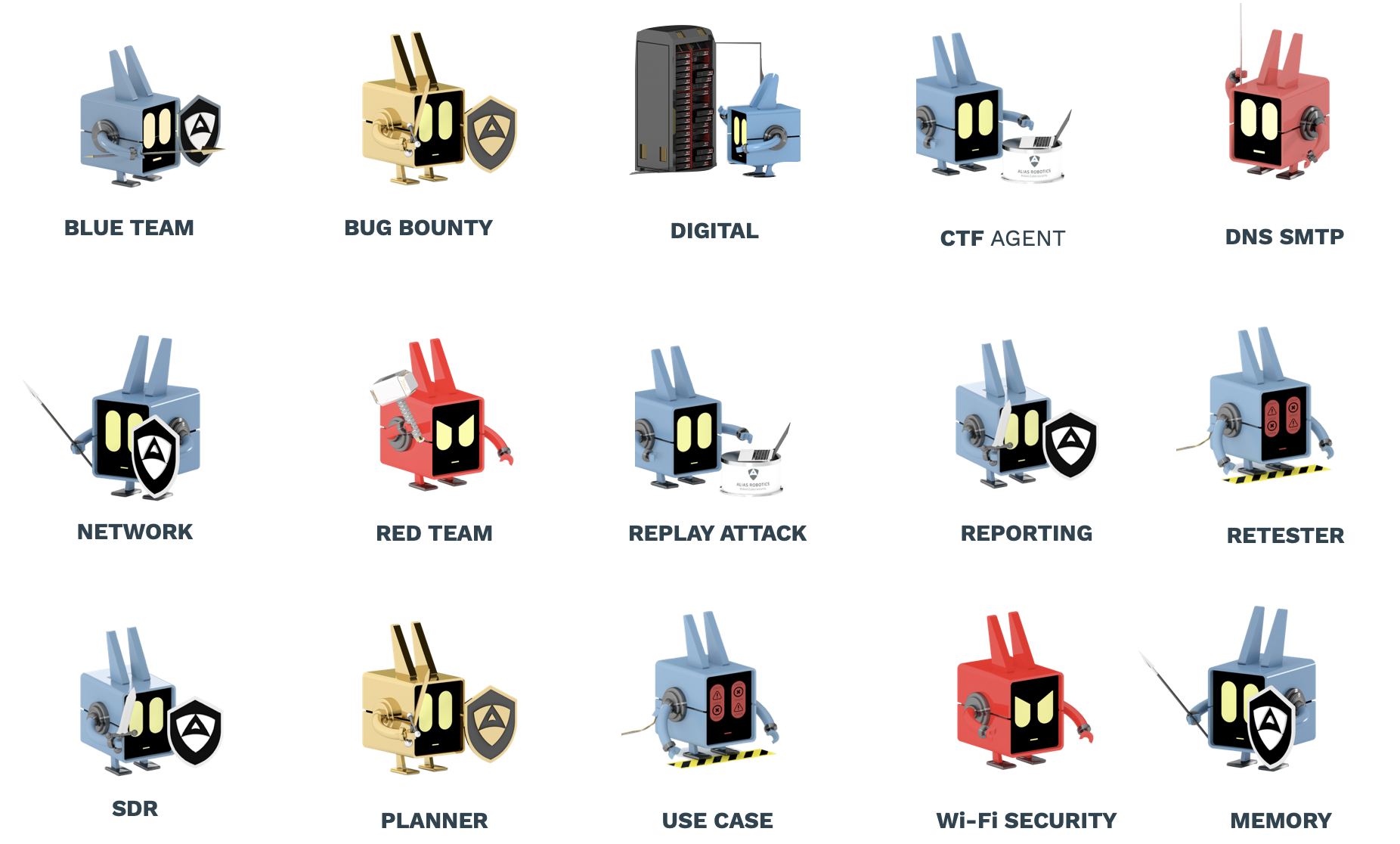
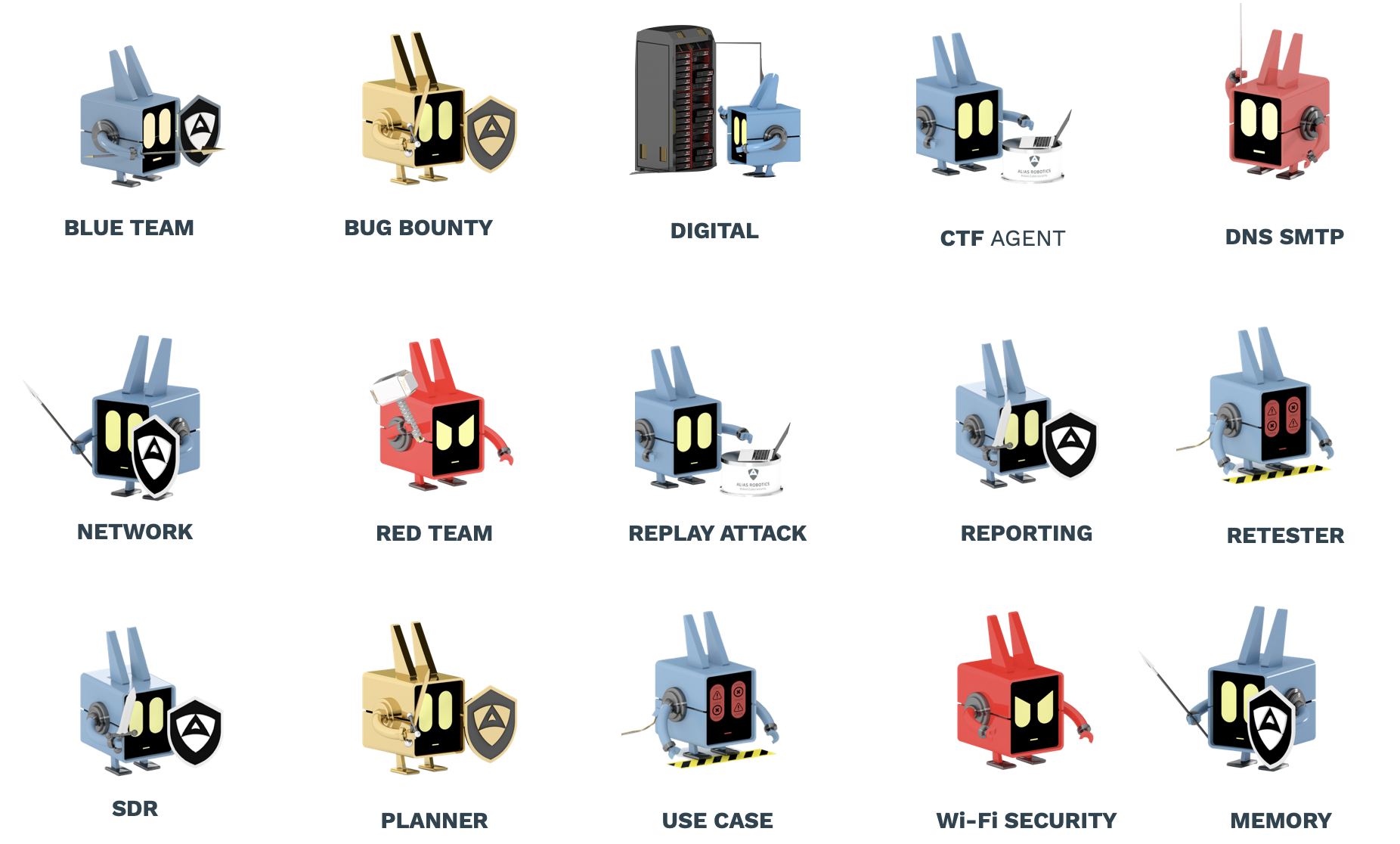
Products
From intelligence to execution. A complete cybersecurity AI stack:
specialized intelligence, CybersecurityAI CLI agent and automated security operations.
Intelligence


Cybersecurity LLM
CybersecurityAI


CybersecurityAI (CLI)
Execution
Automated