Code Testing
for robots
Code testing
for robots
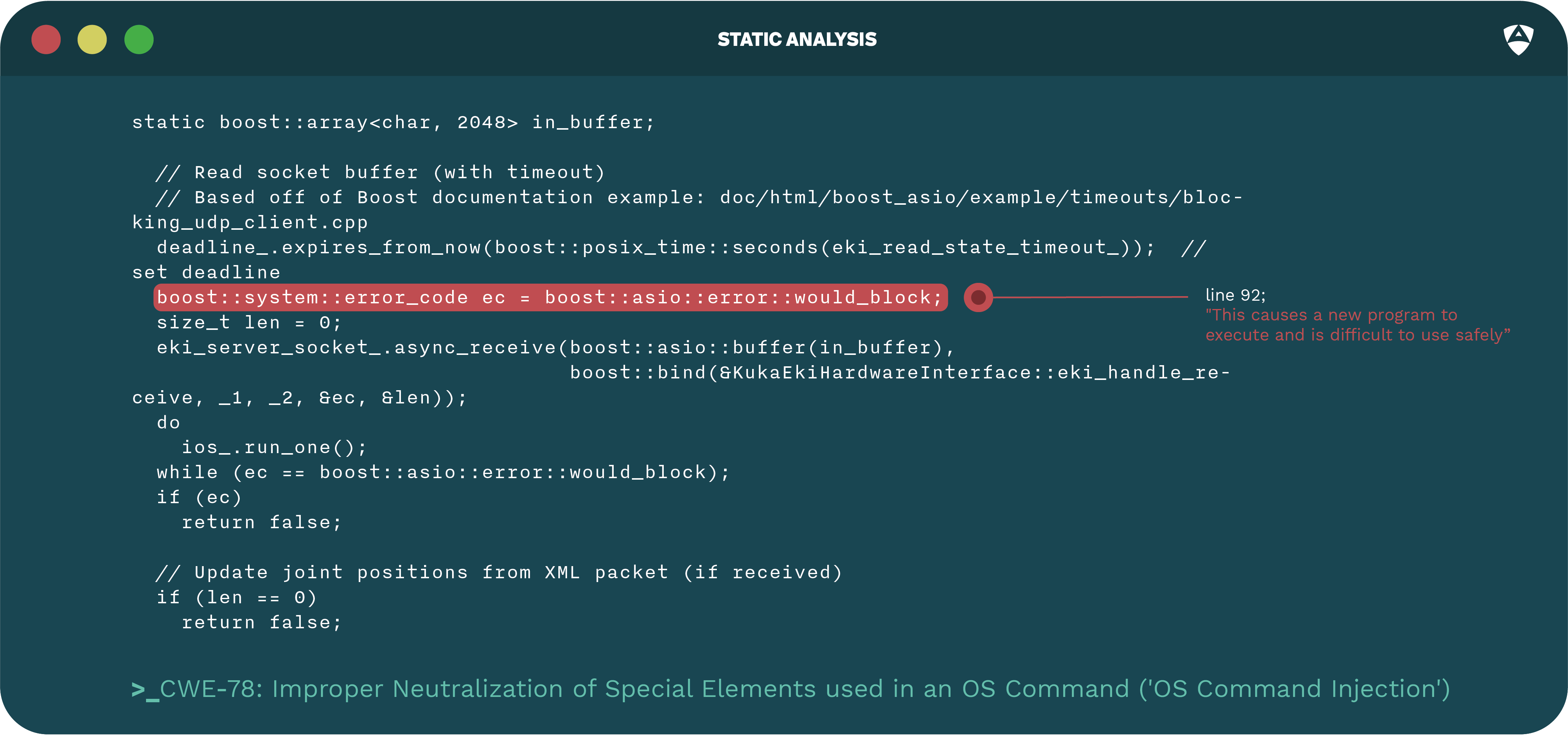
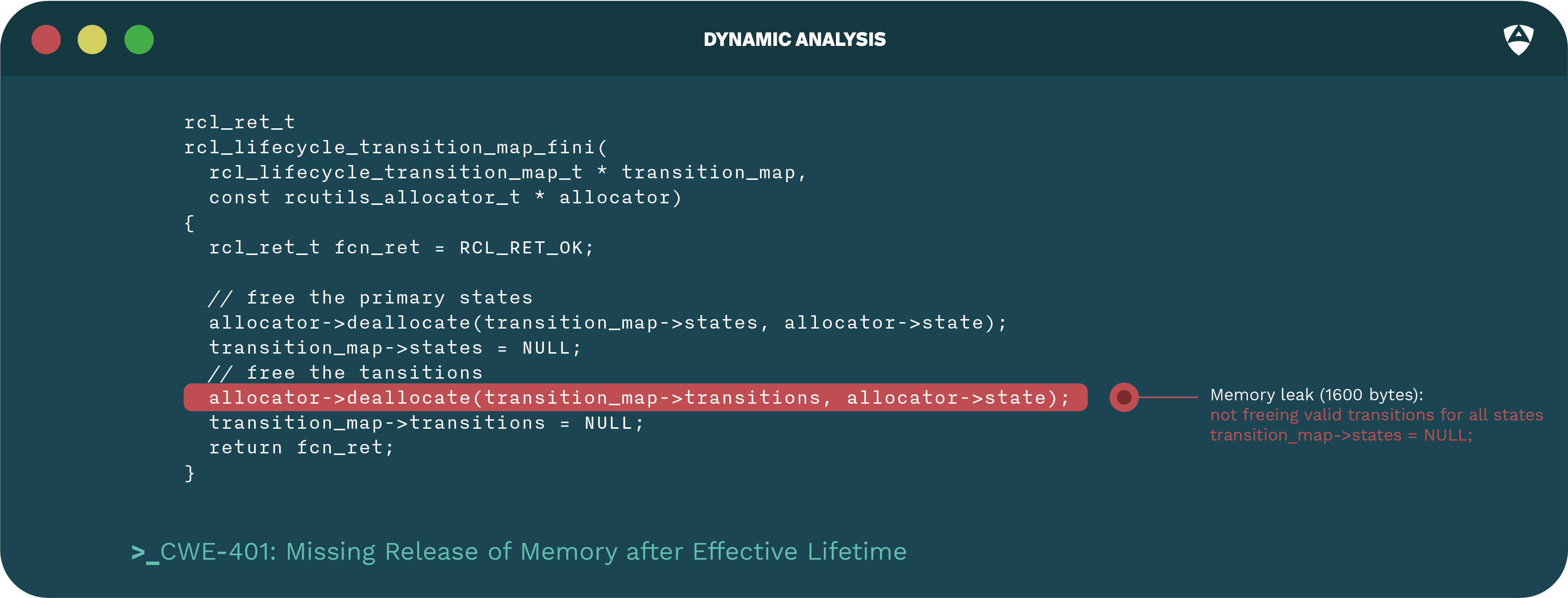
Alias Robotics validates the quality and actively looks for flaws and vulnerabilities within the source code of the robot. We test source code and look for security flaws using a variety of techniques including static and dynamic analysis.
Code testing assessment is generally performed in a white-boxed manner where Alias has complete access to the source code of the robot or robot component.
See how it is done
Get now!